Smart Factory Cybersecurity: 5 Common Mistakes to Fix in 2026
Smart factories fail at cybersecurity when they overlook the risks of connecting legacy industrial equipment to the internet. This gap between Information Technology (IT) and Operational Technology (OT) creates vulnerabilities that hackers exploit. Fixing this requires network segmentation, rigorous patching, and continuous monitoring to protect the entire production line.
Why is IT/OT convergence a security risk?
For decades, the manufacturing world lived by a simple rule: the factory floor (Operational Technology) was physically separated from the office computers (Information Technology). This was the "air gap." But as we move further into 2026, that gap has completely vanished in Tennessee’s smartest factories. While this connectivity allows for incredible real-time data and efficiency, it also opens a digital doorway for threats to walk right through.
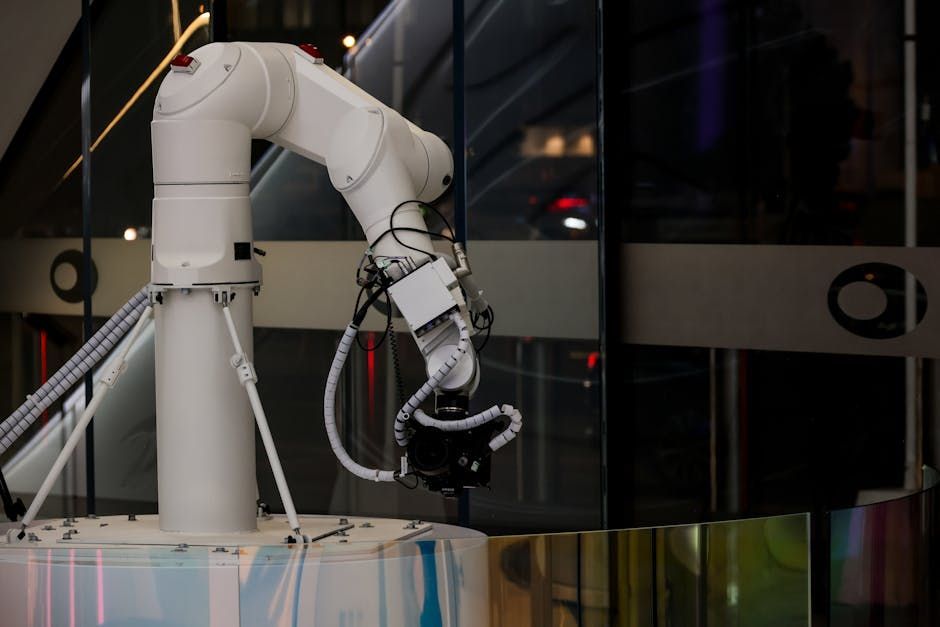
When you connect a CNC machine or a robotic arm to your primary network, a single phishing email in the accounting department can suddenly become a ransomware attack that halts your entire assembly line. Many manufacturing CEOs assume their shop floor is safe because it uses specialized protocols, but modern malware is increasingly designed to translate those industrial languages. This convergence is the number one reason smart factories are struggling to keep up with cyber threats.

The danger of the "set it and forget it" mentality
In the world of managed IT services for manufacturing, we often see a dangerous trend: buying high-tech machinery and assuming the manufacturer built security into the hardware. Unfortunately, security is rarely the top priority for industrial equipment designers. They prioritize uptime, speed, and durability.
This leads to several common oversights:
- Default passwords that are never changed after installation.
- Firmware that hasn't been updated since the machine left the crate.
- Diagnostic ports left open for remote vendor access.
- Lack of encryption on internal data transmissions.
- No logging of who accessed the machine's control software.
Are your IIoT devices actually secure?
Industrial Internet of Things (IIoT) sensors are the backbone of the modern smart factory. They track temperature, vibration, and output, feeding that data into your analytics. However, these tiny devices are often the weakest link in your security chain. Because they have limited processing power, they frequently lack the robust encryption needed to fend off even basic attacks.
If an attacker gains control of an IIoT sensor, they can do more than just steal data. They can feed false information to your control systems, leading to equipment damage or unsafe working conditions. For manufacturers in East Tennessee, protecting these devices isn't just about data; it's about physical safety and asset protection. This is where managed IT security services become essential for identifying these hidden gaps.
Why uptime shouldn't override security protocols
We get it—if the line isn't moving, you aren't making money. In the manufacturing sector, "uptime is king" is the mantra. But many smart factories get into trouble because they view security as a barrier to productivity. They might skip a critical software patch because it requires a two-hour reboot, or they might give every operator administrative access to avoid call-outs at 2:00 AM.
This short-term thinking often leads to long-term disasters. A planned two-hour maintenance window is much cheaper than a three-week shutdown due to a ransomware attack. CEOs and owners need to shift their perspective: cybersecurity is a component of reliability, not an obstacle to it. Integrating security into your IT consulting and strategy ensures that protection happens alongside production, not in spite of it.

Modernizing legacy systems without breaking production
One of the biggest hurdles for Tennessee manufacturers is the age of their equipment. You might have a multi-million dollar machine that is 20 years old and runs on Windows XP. It still does its job perfectly, but it is a massive security liability. You can't just "patch" an OS that has been end-of-life for a decade.
Instead of replacing these machines, smart factories are turning to "virtual patching" and isolation. By placing these legacy assets behind specialized firewalls and strictly controlling who can communicate with them, you can extend their life without exposing your entire network. This approach requires a deep understanding of endpoint management to ensure that even the oldest gear doesn't become the newest entry point for hackers.
How can managed IT support protect your production line?
Managing the complexity of a smart factory is a 24/7 job that most internal teams aren't equipped to handle alone. Between monitoring for intrusions and managing data backup and recovery , the workload is immense. Partnering with a specialized provider brings several advantages to the shop floor.
- Real-time threat detection across both IT and OT networks.
- Strategic planning for legacy equipment isolation and protection.
- Automated patching schedules that respect production windows.
- Incident response plans tailored to manufacturing recovery times.
- Continuous compliance auditing for industry-specific regulations.
Conclusion: The path to a secure smart factory
Cybersecurity in a smart factory isn't about buying a single piece of software; it’s about a cultural shift that recognizes the risks of a connected floor. By addressing the convergence of IT and OT, securing IIoT devices, and refusing to let uptime compromise safety, manufacturers can thrive in the digital age. Don't wait for a breach to realize that your
Recent Posts